Sometimes there is a confusion between Identification and Authentication. So in this article I want to touch on Identification and Authentication then discuss the factors of authentication.
What is the difference between Identification and Authentication?
What is the difference between Identification and Authentication?
- Identification is normally the way to describe a user, or principal, such as a username, email, etc. "I am Bob"
- Authentication is a way of proving and confirming the user, or principal is who they say they are. "I am Bob because my password is ****"
- An additional term that may come up when looking at Identification and Authentication is Non-Repudiation which is to ensure that a transferred message has been sent and received by the parties claiming to have sent and received the message. This guarantees that the sender of a message cannot later deny having sent the message and that the recipient cannot deny having received the message.
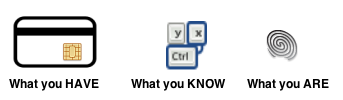
What are the Authentication Factors
Type 1
Type 1 is normally the Knowledge Factor that describes things only the user knows. Examples are:
- Passwords
- PINs
- Passphrases
Because of weak passwords, brute force password hacking and password recovery techniques, Multifactor authentication is being offered more frequently to counteract hacking threats. We will touch on that in a moment.
Type 2
Type 2 is normally the Ownership Factor that describes something you have. Examples are:
- Token Devices
- Cryptographic Keys
- Smart Cards
Type 3
Type 3 is normally the Inherence Factor that describes something you are. Examples are usually around biometrics such as:
- Fingerprints
- Retinal Scans
- Iris Scans
- Hand Geometry
- Voice
Type 4
Type 4 is a new Factor that has been introduced that describes where you are or my location. Examples are usually Real Time Locating Systems (RTLS):
- Personal Tag Beacons
- GPS Devices
Multi-factor
Multi-factor authentication (MFA) enforces at least 2 of the authentication factors such as a password and fingerprint. So MFA combines 2 or more independent credentials. Requiring more than 1 factor usually decreases the ease of hacking or providing false credentials which in turn improves security and reduces data theft. Examples include:
- Swiping a card and entering a PIN.
- Logging into a website and being requested to enter an additional one-time password (OTP) that the website's authentication server sends to the requester's phone or email address.
- Swiping a card, scanning a fingerprint and answering a security question.